If you are unable to Hack WPA / WPA2 WiFi network using WPS Feature, then you have to crack actual WPA / WPA2 encryption. In this hacking process, handshake packets are the only packets which helps in cracking the network. They contain data that can be used to check that WiFi password / key is valid or not. Handshake packets are the 4 packets, which are communicated between the client and the router, when the client connects to the network. These handshake packets can be used to crack WPA / WPA2 key.
- WPS can be enabled using the following 2 choices: 1. Hardware WPS button: This method makes wireless connection as simple as pushing a button on the Wi-Fi enabled device and the wireless router. Take Edimax wireless router as an example, simply pushing the WPS button for 5 seconds and clicking the WPS button of the wireless card completes the.
- UPDATE: The BEST Dictionaries & Wordlist for WPA Cracking. This is a 18 in 1 WPA Edition Password List, its not only a combination of Passwords: Merged each 'collection' into one file (minus the 'readmes' files) Removed leading & trailing spaces & tabs. Converted all 'new lines' to 'Unix' format. Removed non-printable characters.
Steps to Hack WPA / WPA2 WiFi Network using Word List Attack
Enable Monitor Mode of Wireless Interface Card.
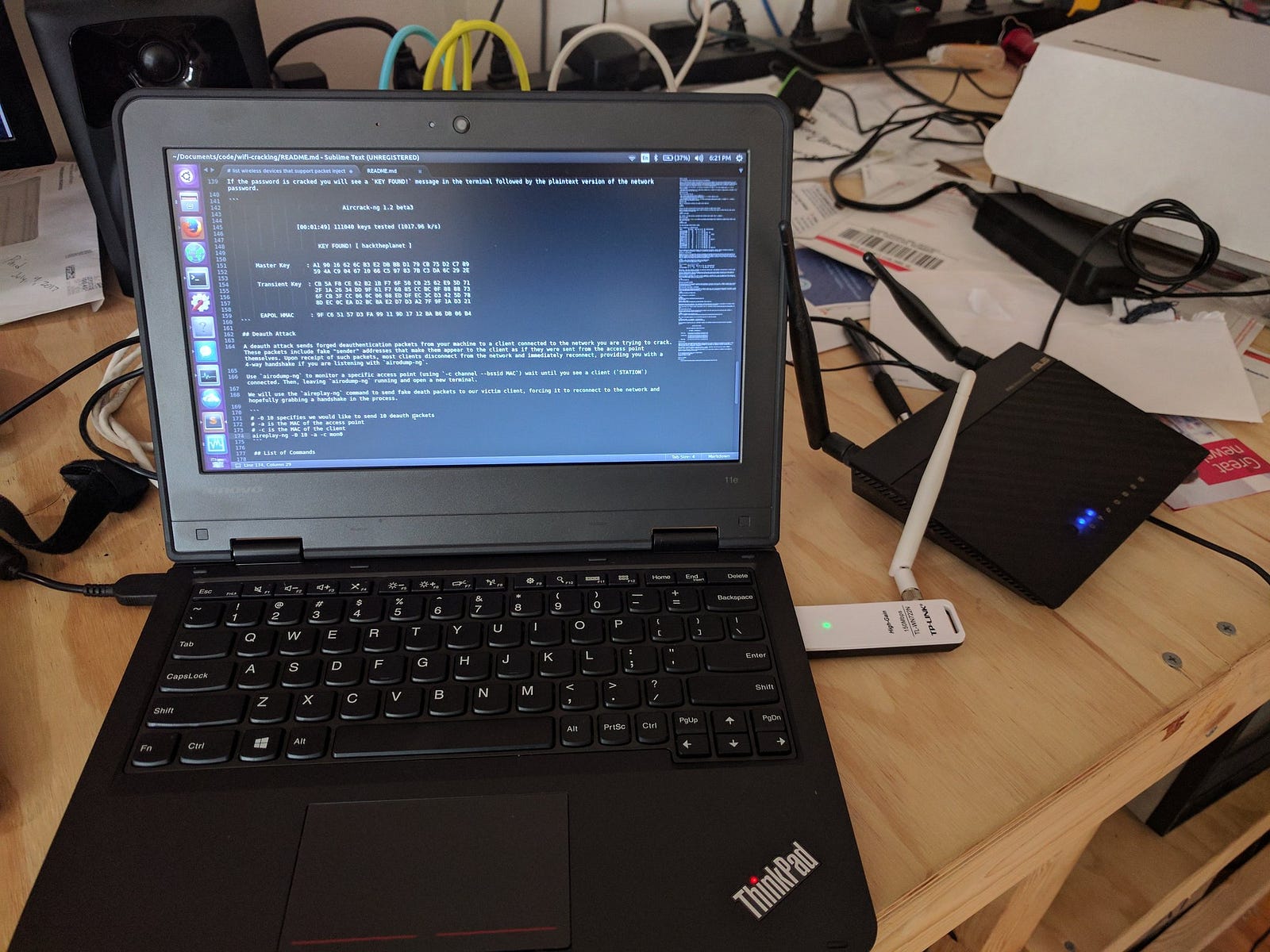
Capture handshake packets using airodump-ng in Kali Linuxagainst your target network and store the data in a file called hack_wpa_handshake.
Now wait for the handshake packets to be captured. Handshake packets will only be sent when a new client is connected to the network. So, wait until new client is connected to the network.
OR
Alternatively you can use De-authentication Attack, where existing client is disconnected from the network and that client will automatically try to connect to the network again. Once that client is re-connected, handshake packets will be send in the air and then we can capture those handshake packets.
Once the new client is connected to the network or the existing client is disconnected and reconnected to the network, we will receive WPA handshake which is stored in a file called hack_wpa_handshake
Create a word list that contains the large number of passwords / keys
.
Once we have a handshake packet, we will create a word list document that contains password. This document is created usingcrunchtool.Go through the passwords in word list document one by one and use them with the handshake to check that whether password in the document is valid or not.
Use handshake packets to crack WPA/WPA2 password
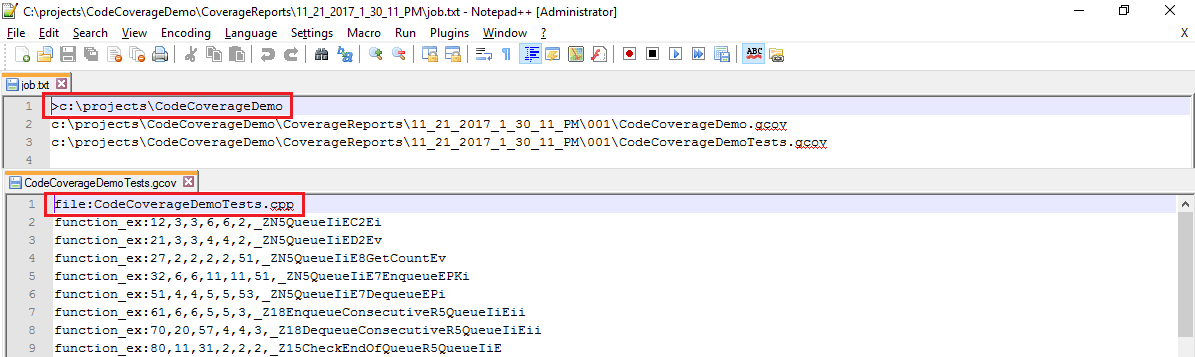
For cracking WPA/WPA2 password, we will use tool named aircrack-ng. Aircrack-ng will unpack the handshake packet and will match the wordlist passwords one by one with the handshake packet.
There are multiple ways to crack WPA/WPA2 passwords using wordlist attack. Some save the cracking progress and some does not save the cracking progress.
Use aircrack-ng to run wordlist attack to crack WPA/WPA2 passwords without saving cracking progress
In the above command:
- aircrack-ngis the name of the program
- hack_wpa_handshake-01.capis the handshake file which we captured before
- -w PasswordList.txtis the name of my word list document, which contains large number of passwords
aircrack-ng tool runs through the word list document, match each word in the word list with the handshake packet one by one. And at the end, we are able to find the key “abc12345” which is our WiFi network key
For big word list documents, it may takes many hours / days to try all the possible passwords. There could be much bigger dictionaries, that can take many many days to crack the passwords. If we quit aircrack-ng during the process and run the command again, it will lose the session and will start the cracking session from scratch.Save cracking progress while cracking WPA/WPA2 passwords using John the Ripper
In this attack, we will save the cracking session while running aircrack-ng command. So, if we quit aircrack-ng and come back after some time then our session will still be there and we can start the session from where we left. We can save our cracking session usingpassword cracking tool named john the ripper
Here
- johnis the name of the password cracking tool
- –wordlist=PasswordList.txtis the name of the wordlist, which is stored in our current working directory
- –stdoutdisplay this wordlist on the terminal screen
- –session=hackrouter will store the session of john the ripper. Session name is hackrouter
- |using this pipe character (vertical bar), we will redirect the wordlist output and use it as an input to aircrack-ng
- -w – , in this -w attribute, we normally gives the wordlist document name but this time we will use the output generated by john command. And this can be done by using just the – (dash) instead of the wordlist document name
- -b 62:23:6A:96:69:73is the MAC address of my target network
- hack_wpa_handshake-01.capis the name of the handshake file
When john the rippercommand run, it will read all the passwords from a file PasswordList.txt, it will pipe them into aircrack-ng . Aircrack-ng will read these passwords and start cracking. Then when we exit at the middle, john the ripper will store this session in a file named hackrouter.
Now next step is to resume the session using this command
In the above command, we are telling john the ripper to restore the session from where it left last time. And this is stored in a session named hackrouter. This method allows you to stop the attack and start the attack whenever you want.
Lista de pines wps para el software de auditoria de redes wifi Dumpper. En el archivo PinList.txt encontraras un recopilado de Pins WPS en formato para el programa Dumpper. List of wps pins for Dumpper Wi-Fi network audit software. In the PinList.txt file you will find a collection of WPS Pins in format for the Dumpper program.
Product Description
Quanta Computer Incorporated is a Taiwan-based manufacturer of electronic hardware.It is the largest manufacturer of notebook computers in the world.
Vulnerabilities Summary
The Quanta LTE QDH Router device is a LTE router / access point overall badlydesigned with a lot of vulnerabilities. It's available in a number of countries toprovide Internet with a LTE network.
The tests below are done using the latest available firmware (firmware 01.00.05_1210, model revision QDHY10_M1.2252_45041, /DailyBuild/MDM9x25_2031_QDT/QDHY_2031_YOOMEE/codebase/MDM9x25_2031_QDH_20141210_0940/MDM9x25_2031_QDT/LINUX/apps_proc/oe-core/build/tmp-eglibc/work-shared/gcc-4.6.2+svnr181430-r22/gcc-4_6-branch/libgcc/../gcc/config/arm).
The summary of the vulnerabilities is:
A personal point of view: at best, the vulnerabilites are due to incompetence; at worst, it is a deliberate act of security sabotage from the vendor. Not all the vulnerabilities found have been disclosed in this advisory. Only the significant ones are shown.
Note: This firmware is being used by other Quanta CPEs. From the /usr/www/js/ui/qdisplay.js file,the vulnerable firmware seems to be used in several routers:
- Quanta 4G WiFi Router QDH
- Quanta 4G WiFi Router UNE
- Quanta 4G WiFi Router MOBILY (QDH-Mobily - CPE342X)
- Quanta 4G WiFi Router Yoomee
The routers are still on sale and used in several countries.
Due to lack of communication of the vendor, the specific list of affected countries is unknown. However, we assume the affected firmware is used at least in some Arabic speaking countries as the Help files are written in English, French, Chinese and Arabic (See http://192.168.1.1/help_ar.html).
Due to lack of security patches provided by the vendor, the vulnerabilities will remain unpatched.
Details - Hardcoded SSH Server key
A hardcoded SSH server key can be found in /etc/dropbear/dropbear_rsa_host_key and can be used to decipher SSH traffic to the router:
Base64 hardcoded SSH server key:
Details - Backdoor accounts
By default, telnetd and SSHd are running in the router.
2 backdoors accounts exist and can be used to bypass the HTTP authentication used to manage the router.
The password for admin is 'admin' and can be found in the /bin/appmgr program using IDA:
About the root user:
Using john to crack the hashes:
Results:
- admin has password admin
- root has password 1234
Working exploit for admin:
Alternatively, you can fetch it at https://pierrekim.github.io/advisories/quanta-ssh-default-password-admin.
Working exploit for root
Alternatively, you can fetch it at https://pierrekim.github.io/advisories/quanta-ssh-default-password-root.
Details - Router DoS
The router has apparently small capacity when trying to route packets.
This 'exploit' will likely force the router to reboot:
Alternatively, you can fetch it at https://pierrekim.github.io/advisories/quanta-dos-crash-router.sh.
Details - WebInterface Information Leak
The webinterface allows an attacker to retrieve every sensible information without authentication (web login, web passwords, wifi configuration, WPS PIN, Dyndns login, Dyndns passwords, Wifi SSIDs, ...).
This 'exploit' will show all the configuration of the router, including logins and passwords:
Alternatively, you can fetch it at https://pierrekim.github.io/advisories/quanta-infoleak.sh.
Using this exploit:
Details - RCE #1
The Webinterface allows an attacker to execute commands as root by injecting commands.
The first RCE has been found in the ping API:
Ping Remote command execution with nc -l -p 1337 -e /bin/ash as a payload
A complete exploit is provided and will produce this output:
This exploit will bypass the authentication, get the information about credentials using the infoleak, use them to get a CSRF token, launch a backdoor shell as root, add an user and then connect with SSH with the new created account with a fully-working shell:
Alternatively, you can fetch it at https://pierrekim.github.io/advisories/quanta-rce-remote-exploit-ping.sh.
Details - RCE #2
The Webinterface allows an attacker to execute commands as root by injecting commands.
The second RCE has been found in the traceroute API:
Traceroute Remote command execution:
Working exploit:
The output is the same as the first RCE. A complete exploit is provided and will produce this output:
This exploit will bypass the authentication, get the information about credentials using the infoleak, use them to get a CSRF token, launch a backdoor shell as root, add an user and then connect with SSH with the new created account with a fully-working shell:
Alternatively, you can fetch it at https://pierrekim.github.io/advisories/quanta-rce-remote-exploit-traceroute.sh.
Details - Backdoor
A backdoor is present inside the /bin/appmgr program. By sending a specific string in UDP to the router, an authentication-less telnet server will start if a telnetd daemon is not already running.
In /bin/appmgr, a thread listens to 0.0.0.0:39889 (UDP) and waits for commands.
If a client sends 'HELODBG' to the router, the router will execute /sbin/telnetd -l /bin/sh, allowing to access without authentication to the router as root.
When using IDA, we can see the backdoor is located in the main function (line 389):
Working PoC :
Details - Default WPS PIN
Wi-Fi Protected Setup(WPS) is a standard for easy and secure establishment of a wireless home network, as defined in the documentation provided in the router (help.html).
By default, the PIN for the WPS system is ever 28296607. It is, in fact, hardcoded in the /bin/appmgr program:
An user can check in the webinterface ('Par defaut' means 'By default'):
This PIN can be found in the HostAP configuration too, and, using the information leak, in the HTTP APIs of the router:
Leak of the default WPS PIN in the HTTP APIs:
Details - Weak WPS PIN Generation - with a reverse-engineered algorithm
An user can use the webinterface to generate a temporary PIN for the WPS system (low probability as the 28296607 WPS PIN is provided by default).
The PIN generated by the router is weak as it is generated using this 'strange' reverse-engineered algorithm:
You can fetch this program at https://pierrekim.github.io/advisories/quanta-wps-gen.c.
Using srand(time(0)) as a seed is a bad idea because an attacker, knowing the current date as time(0) returns the current date in an integer value, can just generate the valid WPS PIN. The Router uses NTP so is likely to have a correct timestamp configured. It's trivial for an attacker to generate valid WPS PIN suites and bruteforce them.
For the curious reader, the original algorithm in the firmware is:
Details - Backdoor accounts in Samba
Samba is configured to run by default and the /bin/genpasswd program configures the different accounts.
As seen in the IDA screenshot, multiple backdoors accounts are created:
- admin with the password 1234
- support with the password 1234
- user with the password 1234
- nobody with the password 1234
From /bin/genpasswd:
The resulting file (/usr/pc/samga/etc/passwd) is:
And john confirms the passwords:
WPSPin-v1.0.3.apk
When Samba starts, the passwd file is copied into /var/pc/samba/etc/passwd.
Details - Leaking No-IP account (?):
The file /etc/inadyn-mt.conf (for a dyndns client) contains an user and a hardcoded password. I don't know if it is used:
Details - Remote FOTA (Firmware Over The Air)
The credentials to contact the FOTA server are hardcoded in the /sbin/fotad binary, as shown with this IDA screenshot:
The function sub_C8A4 contains the credentials as base64-strings, used to retrieve the firmware.
It's notable the FOTA daemon tries to retrieve the firmware over HTTPS. But at the date of the writing,the SSL certificate for https://qdp:qdp@fotatest.qmitw.com/qdh/ispname/2031/appliance.xml is invalid for 1 year.
The user/password combinaisons are:
Details - TOCTOU vulnerability in QCMAP_ConnectionManager - LPE
This program is started at boot as root. The function sub_131F4 creates the /etc/guest_access_rules.sh file, then fills it with ebtables commands, then chmod 777 /etc/guest_access_rules.sh (!), then executes /etc/guest_access_rules.sh (as root) and then removes it from the filesystem.
The local admin user (without root privileges) can use this TOCTOU vulnerability to gain root privileges in the router. Chmoding 777 a file and then executing it as root doesn't seem to be a good idea.
ds_system_call() is a wrapper to system().
Beginning of the sub_131F4 function (/etc/guest_access_rules.sh is opened and ebtables are created):
End of the sub_131F4 function, where the TOCTOU vulnerability is located:
The attentive reader will comment that the program doesn't check if the file /etc/guest_access_rules.sh already existed and if it was owned by a non-root user before doing a fopen (file, 'w'), so this user would keep the rights on the file during all the execution of the function, allowing him to add some commands into the file. He will be right to note this is not a best security practice.
Details - Default Wifi Password Weakness
By default, Wifi password is provided as a 8-char string. It's composed of [A-Z]{8}. It's possible to bruteforce it very fast using a WPA handshake.
Details - HTTP DoS
By sending multiple authenticated http requests to a webservice allowing to retrieve anti-csrf tokens (security feature!), it is possible to get the qmiweb daemon (http daemon) to use 100% of CPU and to become unresponsive.The service doesn't check the number of requested anti-csrf tokens by the client, so it is possible to request a large number of tokens, resulting in the blocking of the HTTP server.
Problematic HTTP request:
PoC:
Alternatively, you can fetch the exploit at https://pierrekim.github.io/advisories/quanta-dos-http.sh.
In the router, the /bin/qmiweb program uses all the CPU.
Details - Arbitrary file browsing using the http daemon
If an usb key or an usb hard disk is connected to the router, then it's possible to do arbitrary browsing using the http daemon in file system of the router using root privileges.
The problem is the function in the http daemon which doesn't clean ../../ in the HTTP requests.
Using the provided exploit: the exploit uses the information leak to use the login/password to get a valid cookie session and then exploits the vulnerability in the http daemon.
PoC to browse the / directory of the router:
Source of the exploit:
Alternatively, you can fetch the exploit at https://pierrekim.github.io/advisories/quanta-http-directory-listing.sh.
Details - Arbitrary file reading using the http daemon

If an usb key or an usb hard disk is connected to the router, then it's possible to do arbitrary file reading in the file system of the router using root privileges.
The problem is the function in the http daemon which does clean the ../../ strings in the requests but not hex-encoded '/' (%2f) characters.
Using the provided exploit: the exploit uses the information leak to use the login/password to get a valid cookie session and then exploits the vulnerability in the http daemon.
PoC to retrieve the /etc/shadow file:
Source of the exploit:
Alternatively, you can fetch the exploit at https://pierrekim.github.io/advisories/quanta-http-file.sh.
Details - Network Eavesdropping - Interception with the gglogd program
By default, the available pcap library is not located in the good path and tcpdump doesn't work (missing lib).
The /bin/gglogd program is interesting because it fixes the tcpdump dependencies by moving libpcap into the correct directory, as shown in IDA screenshots.
Then, the /bin/gglogd program will log all the traffic passing through the bridge0 (wlan0+eth* : wireless and ethernet) and the LTE interface (rmnet0). The resulting interception files will be written into the flash memory, so 'somebody' can retrieve the logged traffic even if the router is rebooted.
Fixing tcpdump library:
Execution of tcpdump:
/bin/gglogd is not started by default but it is suspicious that (1) this kind of the program is present in this router, (2) the program will fix the tcpdump dependencies on its own (tcpdump doesn't work by default in the firmware image) and (3) intercepting files are stored in a persistent storage. This intrigues further thoughts what the developer wanted to achieve from these settings.
This is not a vulnerability but an interesting fact.
Details - Misc
Samba is started if a FAT32 usb disk is connected. The provided Samba version (3.0.25b) is outdated : 9 year old and is prone to =~ 28 CVEs allowing an attacker to execute arbitrary code as root. I advise users not to connect usb disks to this device, connecting an usb disks will start the samba daemons.
Dropbear is outdated (v2011.54).
Details - Security removed in UPnP
UPnP allows to add firewall rules dynamically. Because of the security risks involved, generally there are restrictions in place to avoid dangerous new firewall rules from an unstrusted LAN client.
Insecurity in IPnP was hype 10 years ago (in 2006). The security level of the UPNP program (miniupnp) in this router is lowered volontary as shown below and allows an attacker located in the LAN area to add Port forwarding from the Internet to other clients located in the LAN:
From /var/miniupnpd.conf:
There is no restriction about the UPnP permission rules in the configuration file, contrary to common usage in UPnP where it is advised to only allow redirection of port above 1024:
Normal config file:
In the configuration of the vulnerable router where there are no permission rules, an attacker can forward everything from the WAN into the LAN.From example, an attacker can add a forwarding rule in order to allow traffic from the Internet to local Exchange servers, mail servers, ftp servers, http servers, database servers...In fact, this lack of security allows a local user to forward what they want from the Internet into the LAN as shown below with the miranda tool.

Firewall rules in the router before an attacker (with IP 192.168.1.2) uses UPnP:
Firewall rules in the router after an attacker (with IP 192.168.1.2) uses UPnP:
A new firewall rule allowing traffic from the Internet to a local HTTP server (192.168.1.101) was sucessfully added.
Details - Undocumented diagnostic webpage
The webpage at http://192.168.1.1/diaglogs_page.htm (needs a valid session) gives new parameters to edit:
- QXDM Filter (?),
- Download Mode Configuration when modem crash occured,
- usb_factory_pid,
- Web Redirect(?),
- FOTA test Configuration,
- LTE modem Configuration,
- LTE Band Preferences Configuration,
- SMS Self-Registration Debug Test,
- Sending SMS PDU Test,
- Editing TR069 Configuration,
- WLAN (802.11b, bg, bgn)
This is not a vulnerability but an interesting hidden functionality.
Personal notes
As the router has a sizable memory (168 MB), a decent CPU and good free space (235 MB) with complete toolkits installed by default (sshd, proxy (/bin/tinyproxy -c /var/tproxy.conf), tcpdump ...), I advise users to trash their routers because it's trivial for an attacker to use this router as an attack vector (ie: hosting a sniffing tool, LAN hacking, active MiTM tool, spamming zombie).
The reader must understand that not all the vulnerabilities have been disclosed. There is a lot of interesting undisclosed findings in this router (including RCEs) and I encourage security researchers to analyze the binaries provided by the firmware (We can agree I already did my part).
Given the vulnerabilities found, even if the vendor changes its mind and decides to patch the router, I don't think it is even possible as it needs major rewrites in several main components (the ASM code shows very bad security practices in several binaries).
From my tests, it is possible to overwrite the firmware with a custom (backdoored) firmware. Generating a valid backdoored firmware is left as an exercise for the reader, but with all these included vulnerabilities in the default firmware, I don't think it is worth making the effort.
To illustrate the precedent fact, here is the current available space in the router:
Tribute to Alex
The /var/alex directory is used as a storage directory for logs. This in a non conventional path and seems to be named after one of the programmer's name. Hello Alex !
In Samba:
In the Firmware Over The Air program:
Having fun with the LEDs:
This device has a lot of LEDs and an user can control them.
You can recycle the router as a funny 'light show' device with this command:
The leds will start blinking like crazy. It will add some fun in this long journey.
Vendor Response
The vulnerable router is in the End Of Service cycle and will not be supported anymore.
The vendor considers the router is still working well.
The vendor will consider security in their next product development.
Report Timeline
- Dec 04, 2015: Vulnerabilities found by Pierre Kim.
- Mar 04, 2016: security@quantatw.com is contacted asking for a GPG key to exchange about vulnerabilities: email bounced.
- Mar 04, 2016: Quanta is contacted about vulnerabilities in their routers and how to get a security contact at Quanta.
- Mar 04, 2016: Quanta asks Pierre Kim about the affected device: model name, version and clear details about the vulnerabilities in order to redirect to the good IT department.
- Mar 04, 2016: Pierre Kim specifies the model of the Router, asks for a GPG key in order to send detailed informations and clarifies he found backdoor accounts in the default firmware, allowing an unauthenticated, remote attacker to log in to the device with the privileges of the root user.
- Mar 09, 2016: Pierre Kim contacts Quanta again to get a contact at the security team.
- Mar 12, 2016: Pierre Kim contacts Quanta again to get a contact at the security team.
- Mar 14, 2016: A Sale Account Manager at Quanta ('MIS department') asks if Pierre Kim gets the device from the Operator YooMee and says 'The S/W is already fixed for our customer and we are not able to change it randomly for end customer. However, we appreciate your information and we will take into consideration for the s/w development in the near future.'
- Mar 14, 2016: Pierre Kim asks for clarification and asks if the device is End of Life and unsupported, even for security patches. Pierre Kims asks Quanta about clarification for the Vendor Response in the future public Security Advisory.
- Mar 15, 2016: Quanta confirms the product is EOL and the released firmware was approved by the operator. Quanta can't modify of change without the customer's approval. Quanta does not have plan to patch or change FW as the product is EOL. Quanta thanks Pierre Kim for the information and will consider the findings into our next product development in the near future.
- Mar 15, 2016: Pierre Kim asks if Quanta encourages users to discard the unsupported router for the 'Vendor Response' in the advisory because no patch will be provided by the vendor.
- Mar 16, 2016: Quanta considers the router is still working well but is in End Of Service cycle. Quanta doesn't encourage users to discard the router.
- Mar 16, 2016: Pierre Kim adapts the Vendor Response accordingly but warns Quanta he is very concerned that no security workarounds are provided by the vendor. At this time, Quanta never asked about the security vulnerabilities in detail, nor provided a GPG key.
- Mar 18, 2016: Pierre Kim contacts again Quanta to ask if there is another reachable security team at Quanta. He asks again for a GPG key and demands Quanta to confirm no security patches are planned for the Quanta QDH Router.
- Mar 21, 2016: Quanta confirms the product is EOL. Quanta asks details about the vulnerabilities.
- Mar 22, 2016: Pierre Kim asks Quanta for a GPG key and states he will give a first draft without the exploits if Quanta is unable to provide a GPG key.
- Mar 23, 2016: Quanta asks an advisory in cleartext without exploits.
- Mar 23, 2016: Pierre Kim sends a draft to Quanta.
- Apr 04, 2016: A public advisory is sent to security mailing lists.
WPSPin-v1.0.4.apk
Credit
These vulnerabilities were found by Pierre Kim (@PierreKimSec).
References
Disclaimer
This advisory is licensed under a Creative Commons Attribution Non-CommercialShare-Alike 3.0 License: http://creativecommons.org/licenses/by-nc-sa/3.0/
How To Download Wps Pin List Free - YouTube
published on 2016-04-04 00:00:00 by Pierre Kim <pierre.kim.sec@gmail.com>